File Integrity Monitoring Market Size 2024-2028
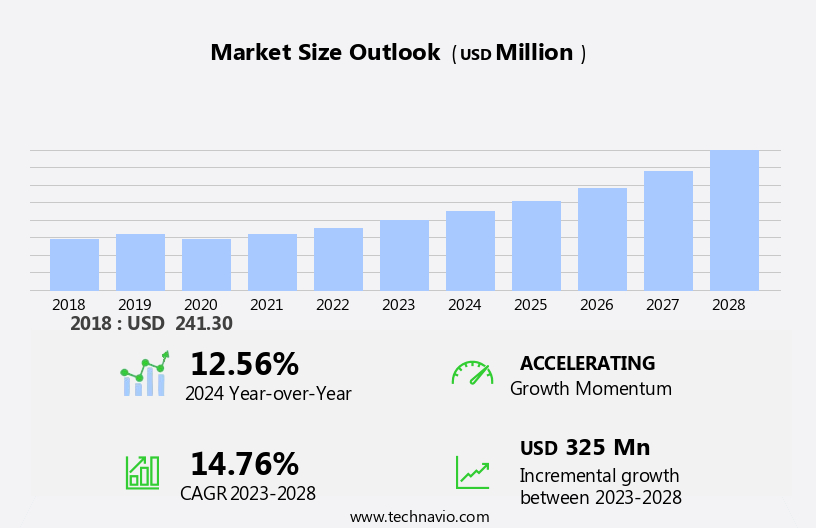
The file integrity monitoring market size is forecast to increase by USD 325 million at a CAGR of 14.76% between 2023 and 2028.
- The File Integrity Monitoring (FIM) market is experiencing significant growth due to the increasing number of data breaches and cyber attacks worldwide. According to recent reports, the global cost of cybercrime is projected to reach USD 6 trillion annually by 2021. FIM solutions have become essential for organizations to safeguard their critical data and maintain system security. Another key driver for the market is the advent of cloud-based antivirus software, which has made FIM solutions more accessible and cost-effective for businesses of all sizes. However, the high cost of maintenance and the complexity of implementing and managing FIM solutions remain challenges for market growth.
- Cloud-based FIM solutions offer a viable alternative to traditional on-premises systems, reducing maintenance costs and providing real-time monitoring capabilities. To capitalize on this opportunity, companies must focus on offering user-friendly and cost-effective FIM solutions that cater to the evolving needs of businesses in various industries. Effective marketing strategies, strategic partnerships, and continuous innovation will be crucial for market players to differentiate themselves and stay competitive In the dynamic cybersecurity landscape.
What will be the Size of the File Integrity Monitoring Market during the forecast period?
- The market is experiencing significant growth as enterprises prioritize securing their sensitive data in an increasingly complex IT infrastructure. Compliances such as PCI-DSS, HIPAA, and SOC 2 require continuous monitoring of operating systems files and application software for any unauthorized changes. Cloud-based deployment and both agentless and agent-based installation modes offer scalability and flexibility for organizations. Capital investment in IT security processes is on the rise, with regulations driving the need for file integrity monitoring solutions. In the e-commerce and financial sectors, where data breaches can result in substantial financial and reputational damage, file integrity monitoring is a critical component of IT security.
- Also, FIM solutions can be deployed in two primary modes: agent-based and agentless. In agent-based installation mode, an agent is installed on each monitored system to collect and transmit data to the management server. The market is also responding to the growing threat landscape, with solutions that employ cryptographic checksums and calculated checksums for validation. The Internet of Things (IoT) and Bring Your Own Device (BYOD) trends add new challenges, as hacktivists and cybercriminals continue to target enterprises.
How is this File Integrity Monitoring Industry segmented?
The file integrity monitoring industry research report provides comprehensive data (region-wise segment analysis), with forecasts and estimates in "USD million" for the period 2024-2028, as well as historical data from 2018-2022 for the following segments.
- End-user
- BFSI
- Government
- Healthcare
- Education
- Others
- Deployment
- Cloud
- On-premises
- Geography
- North America
- US
- Europe
- Germany
- APAC
- China
- India
- Japan
- Middle East and Africa
- South America
- North America
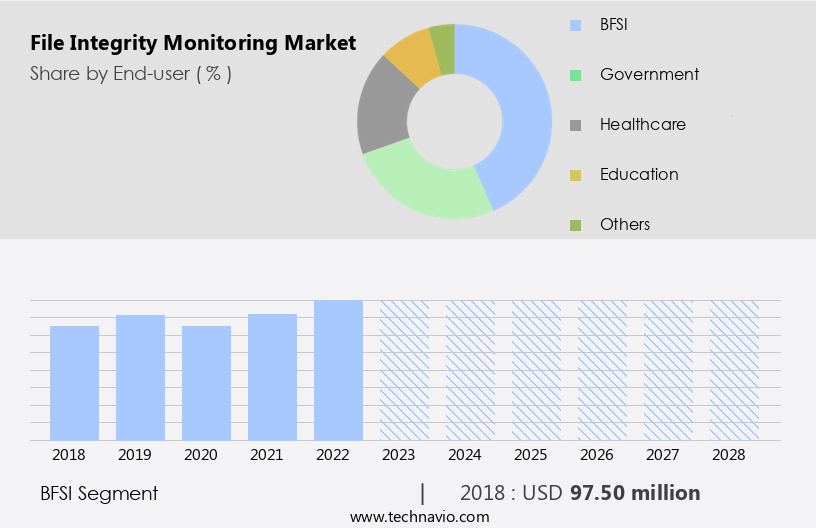
By End-user Insights
The BFSI segment is estimated to witness significant growth during the forecast period.
The BFSI industry, driven by digitalization and customer expectations, leads The market in 2023. With increasing technological advancements and tech-savvy customers, the BFSI sector has shifted its operational landscape, leading to an expanded IT infrastructure and a rise in critical data exchange over virtual networks. This digital transformation In the BFSI industry brings about new risks, such as cyberattacks and fraudulence, which can negatively impact profitability and credibility. To mitigate these risks, the need for file integrity monitoring services is escalating. These services ensure the security and authenticity of critical data by monitoring changes to files and applications in real-time.
Compliance with various regulations, such as HIPAA and PCI-DSS, further focuses on the importance of file integrity monitoring in the BFSI sector. Cloud-based deployment, scalability, and 24/7 services are key features of modern file integrity monitoring solutions, making them an essential investment for enterprises facing IT security challenges under budgetary constraints.
Get a glance at the market report of share of various segments Request Free Sample
The BFSI segment was valued at USD 97.50 million in 2018 and showed a gradual increase during the forecast period.
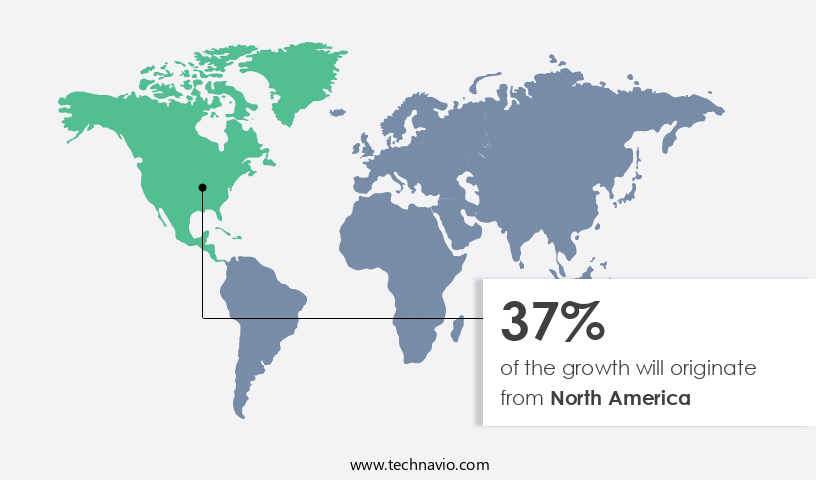
Regional Analysis
North America is estimated to contribute 37% to the growth of the global market during the forecast period. Technavio's analysts have elaborately explained the regional trends and drivers that shape the market during the forecast period.
For more insights on the market size of various regions, Request Free Sample
The File Integrity Monitoring (FIM) market in North America is experiencing significant growth due to the region's early adoption of advanced technologies in industries such as telecommunication, manufacturing, retail, and BFSI. The availability of IT and business infrastructure, stringent IT security compliance and governance regulations, and the high adoption of cloud-based IT security solutions and services are key drivers propelling the market's expansion in North America. Cloud deployment mode is increasingly popular due to its scalability, enabling 24/7 services and reducing the need for hardware, storage, and technical staff. Compliance with regulations, such as HIPAA, PCI-DSS, and SOX, necessitates the use of cutting-edge FIM solutions to ensure data security and integrity.
The market is further fueled by the increasing number of cyber threats, cybersecurity processes, and regulatory reforms, impacting critical infrastructure providers, SMEs, and large enterprises in sectors like healthcare, banking, financial services, insurances, mobile internet users, and young people. Agentless installation mode and agent-based installation mode are also gaining traction, with Bring Your Device, Internet of Things, hacktivists, and cybercriminals posing significant challenges. In summary, the FIM market in North America is poised for growth due to increasing IT security investments, budgetary constraints, and the IT security process's need for authentication, application software, operating systems files, IT infrastructure, internal process validation, cryptographic checksum, calculated checksum, and cybersecurity processes.
Market Dynamics
Our researchers analyzed the data with 2023 as the base year, along with the key drivers, trends, and challenges. A holistic analysis of drivers will help companies refine their marketing strategies to gain a competitive advantage.
What are the key market drivers leading to the rise In the adoption of File Integrity Monitoring Industry?
- Increase in data thefts globally is the key driver of the market. File integrity monitoring services have become essential for enterprises in today's digital landscape, where cyber threats are on the rise. The number of data breaches and files stolen by hackers is increasing globally. For instance, In the US, the Federal Trade Commission (FTC) received approximately 4.8 million identity theft and fraud reports in 2022. File integrity monitoring solutions help enterprises ensure the security of their critical data by verifying user access and managing permissions. These services enable applications to be accessed securely by providing the necessary user information for opening files and accessing data.
- By using file integrity monitoring tools, enterprises can review areas of concern and defend against cyber attacks. File integrity monitoring is crucial in maintaining the security posture of an enterprise. It helps organizations detect unauthorized changes to critical files and systems, providing early warning of potential threats. With the increasing number of cyber attacks, the demand for file integrity monitoring services is expected to grow significantly In the coming years. Enterprises must prioritize implementing file integrity monitoring solutions to protect their valuable data assets.
What are the market trends shaping the File Integrity Monitoring Industry?
- Advent of cloud-based antivirus software is the upcoming market trend. Cloud-based security solutions, including file integrity monitoring, are increasingly adopted by businesses for various applications such as authentication, video management systems, and biometric information storage. With the growing trend of storing large volumes of confidential data In the cloud, particularly in sectors like banking and healthcare, ensuring data security from unauthorized access is paramount. Small and medium-sized enterprises (SMEs) are particularly drawn to cloud-based services due to their cost-effectiveness and lack of requirement for extensive infrastructure. The flexibility and scalability of these solutions cater to the diverse needs of consumers, contributing to their widespread adoption.
- The advent of remote work has led many organizations to implement cloud-based services for business functions like customer relationship management (CRM), payroll, and enterprise communication, enabling employees to access data from anywhere. This shift towards cloud-based services underscores the importance of security measures, including file integrity monitoring, to safeguard sensitive information.
What challenges does the File Integrity Monitoring Industry face during its growth?
- High cost of maintenance is a key challenge affecting the industry growth. File integration monitoring solutions offer enterprises encryption and intrusion detection capabilities for real-time data protection against thefts. However, the high cost of implementing these solutions, including network security firewalls and monitoring platforms, hinders their widespread adoption. The expense of security tools, such as firewalls and detection sensors, can reach up to USD million, while the cost of managing these tools through monitoring platforms can be tenfold.
- The annual maintenance cost of the overall system, which includes hardware support, software support, and signature updates, typically amounts to 60% to 80% of the purchase cost of the firewall equipment. Regular updates are essential for the efficient functioning of firewalls.
Exclusive Customer Landscape
The file integrity monitoring market forecasting report includes the adoption lifecycle of the market, covering from the innovator's stage to the laggard's stage. It focuses on adoption rates in different regions based on penetration. Furthermore, the file integrity monitoring market report also includes key purchase criteria and drivers of price sensitivity to help companies evaluate and develop their market growth analysis strategies.
Customer Landscape
Key Companies & Market Insights
Companies are implementing various strategies, such as strategic alliances, file integrity monitoring market forecast, partnerships, mergers and acquisitions, geographical expansion, and product/service launches, to enhance their presence In the industry.
The industry research and growth report includes detailed analyses of the competitive landscape of the market and information about key companies, including:
- AT and T Inc.
- BeyondTrust Corp.
- Cimcor Inc
- CISO Platform
- Excel Controlinkage Pvt. Ltd
- HelpSystems LLC
- Ionx Solutions LLP
- LogRhythm Inc.
- Microsoft Corp.
- Nagios Enterprises LLC.
- Netwrix Corp.
- New Net Technologies LLC.
- Paessler AG
- Qualys Inc.
- SolarWinds Corp.
- Splunk Inc.
- Tanium Inc.
- Trend Micro Inc.
- Trustwave Holdings Inc.
- Zoho Corp. Pvt. Ltd.
Qualitative and quantitative analysis of companies has been conducted to help clients understand the wider business environment as well as the strengths and weaknesses of key industry players. Data is qualitatively analyzed to categorize companies as pure play, category-focused, industry-focused, and diversified; it is quantitatively analyzed to categorize companies as dominant, leading, strong, tentative, and weak.
Research Analyst Overview
The file integrity monitoring (FIM) market has experienced significant growth in recent years, driven by the increasing importance of data security and regulatory compliance for enterprises. FIM solutions play a crucial role in maintaining the integrity of critical IT infrastructure, including application software, operating systems files, and IT infrastructure. Compliances and regulations have been major factors driving the adoption of FIM solutions. With the increasing number of cybersecurity threats, regulatory bodies have imposed stringent requirements on enterprises to protect their sensitive data. FIM solutions help enterprises meet these requirements by providing real-time monitoring and alerting for any unauthorized changes to critical files.
FIM solutions are available in various deployment modes, including cloud-based and on-premises. Cloud-based deployment mode offers scalability, flexibility, and cost savings, making it an attractive option for many enterprises. However, some organizations prefer on-premises deployment due to concerns over data security and the need for greater control over their IT infrastructure. Capital investment in IT security has been a significant trend In the FIM market. With the increasing number of cybersecurity threats and regulatory requirements, enterprises are investing heavily in security solutions to protect their IT infrastructure and sensitive data. However, budgetary constraints can limit the adoption of FIM solutions for small and medium-sized enterprises (SMEs).
FIM solutions offer 24/7 services to ensure continuous monitoring and protection of IT infrastructure. These solutions use both agent-based and agentless installation modes to monitor files. Agent-based installation mode requires the installation of an agent on each monitored system, while agentless installation mode uses network monitoring to detect changes without the need for an agent. Scalability is another essential factor In the FIM market. FIM solutions must be able to handle large volumes of data and monitor complex IT environments. Hardware and storage requirements can be significant, and technical staff may be needed to manage and maintaIn the FIM solution.
Cybersecurity processes are a critical aspect of FIM solutions. These processes include authentication, validation methods, and cryptographic checksums. Calculated checksums are used to verify the integrity of files, while cybersecurity processes help prevent cyber threats, such as cyberattacks, cyber espionages, and hacktivism. Critical infrastructure providers, including healthcare, banking, financial services, insurances, mobile internet users, young people, e-commerce, and the financial sector, are major users of FIM solutions. These industries handle large volumes of sensitive data and are subject to stringent regulatory requirements, making FIM solutions essential for maintaining data integrity and security. Regulatory reforms have been a significant driver of growth In the FIM market.
Regulations such as the General Data Protection Regulation (GDPR) and the Health Insurance Portability and Accountability Act (HIPAA) have imposed strict requirements on enterprises to protect sensitive data. FIM solutions help enterprises meet these requirements by providing real-time monitoring and alerting for any unauthorized changes to critical files. Organic methods, such as patch management and access control, and inorganic methods, such as acquisitions and partnerships, are used by FIM solution providers to expand their offerings and reach new customers. Cybersecurity attacks, including cyber espionages and cybercriminal activities, continue to pose a significant threat to enterprises, driving the need for advanced FIM solutions to protect IT infrastructure and sensitive data.
In summary, the FIM market is expected to continue growing due to the increasing importance of data security and regulatory compliance for enterprises. FIM solutions offer a range of deployment modes, including cloud-based and on-premises, and provide essential features, such as scalability, 24/7 services, and advanced cybersecurity processes, to help enterprises protect their IT infrastructure and sensitive data. Regulatory reforms and the growing number of cybersecurity threats are expected to drive further growth In the FIM market.
|
Market Scope |
|
|
Report Coverage |
Details |
|
Page number |
158 |
|
Base year |
2023 |
|
Historic period |
2018-2022 |
|
Forecast period |
2024-2028 |
|
Growth momentum & CAGR |
Accelerate at a CAGR of 14.76% |
|
Market growth 2024-2028 |
USD 325 million |
|
Market structure |
Fragmented |
|
YoY growth 2023-2024(%) |
12.56 |
|
Key countries |
US, China, India, Germany, Japan, |
|
Competitive landscape |
Leading Companies, Market Positioning of Companies, Competitive Strategies, and Industry Risks |
What are the Key Data Covered in this File Integrity Monitoring Market Research and Growth Report?
- CAGR of the File Integrity Monitoring industry during the forecast period
- Detailed information on factors that will drive the growth and forecasting between 2024 and 2028
- Precise estimation of the size of the market and its contribution of the industry in focus to the parent market
- Accurate predictions about upcoming growth and trends and changes in consumer behaviour
- Growth of the market across North America, Europe, APAC, Middle East and Africa, South America,
- Thorough analysis of the market's competitive landscape and detailed information about companies
- Comprehensive analysis of factors that will challenge the file integrity monitoring market growth of industry companies
We can help! Our analysts can customize this file integrity monitoring market research report to meet your requirements.


 RIA -
RIA - 
