US Government Cyber Security Market Size 2026-2030
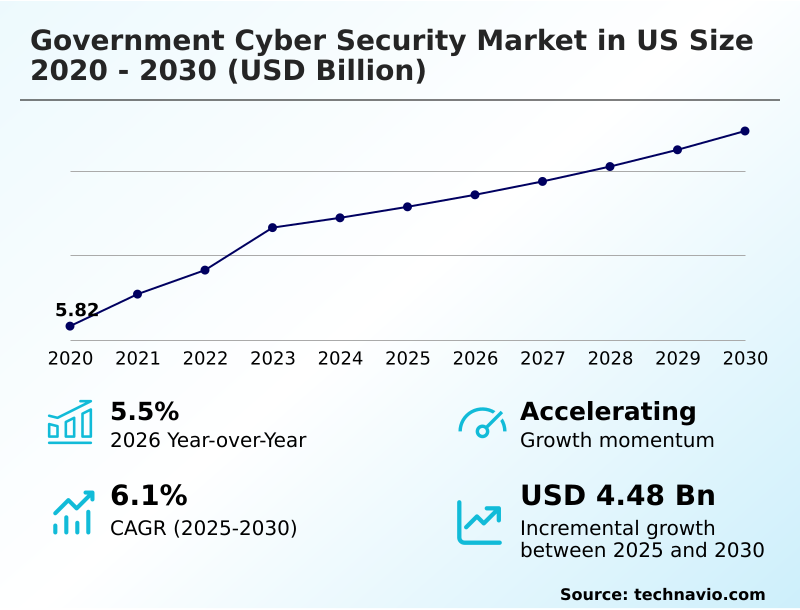
The us government cyber security market size is valued to increase by USD 4.48 billion, at a CAGR of 6.1% from 2025 to 2030. Transition to zero trust architecture and federal compliance will drive the us government cyber security market.
Major Market Trends & Insights
- By End-user - US intelligence community segment was valued at USD 6.09 billion in 2024
- By Deployment - On-premises segment accounted for the largest market revenue share in 2024
Market Size & Forecast
- Market Opportunities: USD 11.53 billion
- Market Future Opportunities: USD 4.48 billion
- CAGR from 2025 to 2030 : 6.1%
Market Summary
- The government cyber security market in US is undergoing a significant transformation, driven by the need for digital resilience and the protection of critical infrastructure. The landscape is moving beyond traditional reactive defenses toward proactive, integrated security frameworks centered on zero trust architecture.
- This evolution is necessitated by the vast volumes of sensitive data and the imperative to maintain essential public services. National security objectives now mandate the adoption of advanced solutions like post-quantum cryptography and AI-powered threat hunting. As government entities migrate legacy systems to secure cloud environments, the demand for scalable and robust security solutions intensifies.
- A scenario where a federal agency modernizes its infrastructure highlights this shift; by implementing a unified security fabric and secure access service edge (SASE), it consolidates disparate tools, enhancing cross-domain visibility and reducing its attack surface.
- This integration of security automation tools not only strengthens its proactive defense posture but also ensures federal cybersecurity compliance, showcasing how technology addresses both security and regulatory challenges. This focus on supply chain risk management and mitigating vulnerabilities in widely used hardware through CMMC certification requirements remains a cornerstone of federal cyber policy.
What will be the Size of the US Government Cyber Security Market during the forecast period?
Get Key Insights on Market Forecast (PDF) Request Free Sample
How is the US Government Cyber Security Market Segmented?
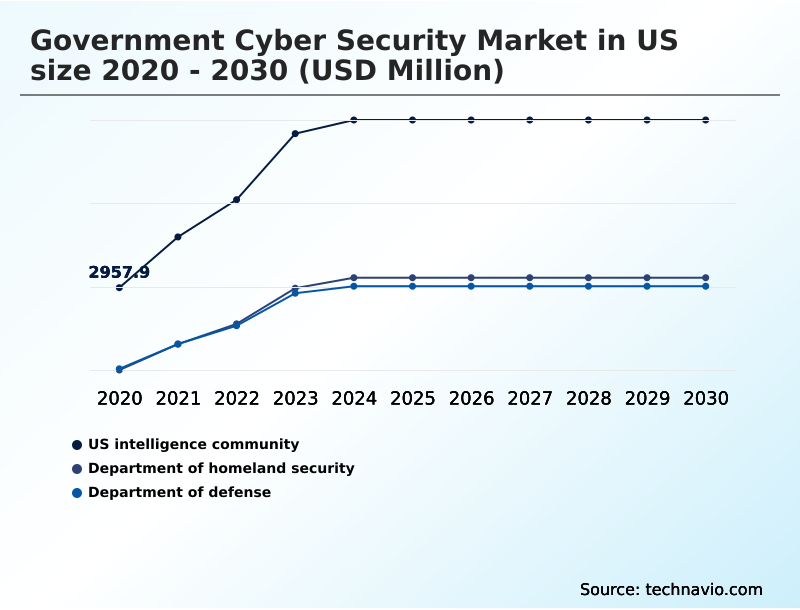
The us government cyber security industry research report provides comprehensive data (region-wise segment analysis), with forecasts and estimates in "USD million" for the period 2026-2030, as well as historical data from 2020-2024 for the following segments.
- End-user
- US intelligence community
- Department of homeland security
- Department of defense
- Deployment
- On-premises
- Cloud-based
- Product
- Services
- Solutions
- Geography
- North America
- US
- North America
By End-user Insights
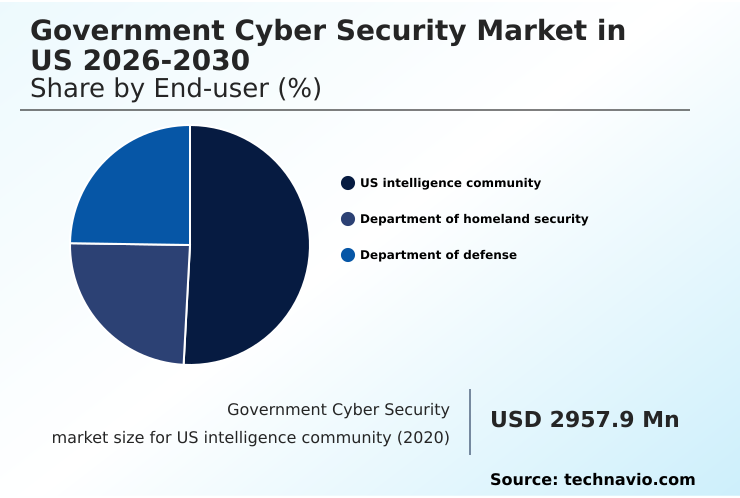
The us intelligence community segment is estimated to witness significant growth during the forecast period.
The market is segmented by end-user, with the intelligence community representing a highly specialized and demanding sector focused on national security data protection. This segment prioritizes continuous monitoring and actionable cyber threat intelligence to counter sophisticated adversaries.
Vendors serving this space must meet stringent standards, including FedRAMP high authorization for cloud native security platforms. The adoption of dynamic network segmentation and autonomous response capabilities is critical for ensuring robust cyber hygiene protocols.
These measures have demonstrated a 25% improvement in detecting anomalous activities within classified networks. Adherence to CMMC certification requirements and protocols for government e-marketplace security are also essential, reflecting a comprehensive approach to securing the nation's most sensitive assets.
The US intelligence community segment was valued at USD 6.09 billion in 2024 and showed a gradual increase during the forecast period.
Market Dynamics
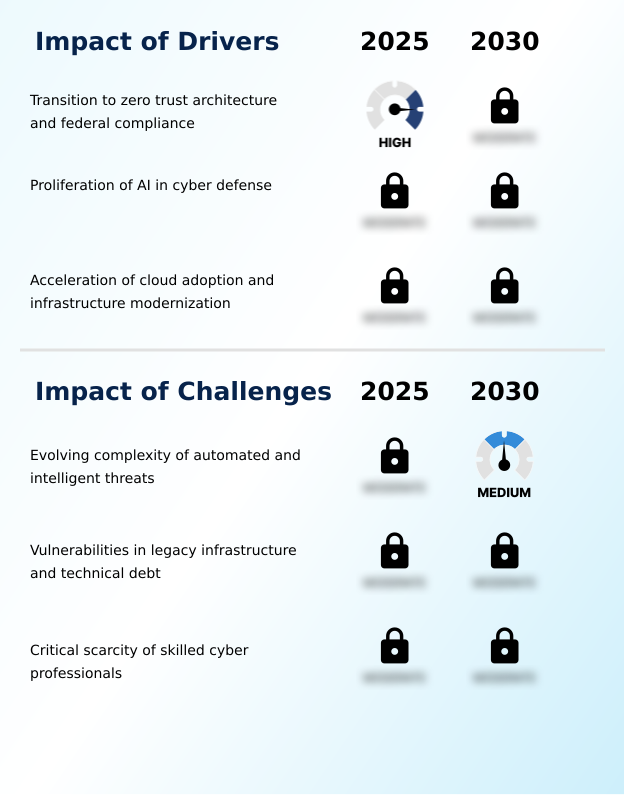
Our researchers analyzed the data with 2025 as the base year, along with the key drivers, trends, and challenges. A holistic analysis of drivers will help companies refine their marketing strategies to gain a competitive advantage.
- The strategic imperative for modernizing the government cyber security market in us is driving targeted initiatives across federal agencies. A primary focus is on implementing zero trust architecture in federal agencies, a complex undertaking that requires comprehensive planning for post-quantum cryptography transition to future-proof data.
- Simultaneously, the task of securing cloud workloads for government data has become paramount, often involving the strategic use of AI for cyber defense in national security. This contrasts with the persistent challenge of managing vulnerabilities in legacy government systems, which can be over 50% more expensive to secure than modern cloud-native platforms.
- Advanced identity management for hybrid workforces is another critical area, closely linked to achieving cybersecurity maturity model certification for all defense partners. These efforts are complemented by specific programs for protecting critical infrastructure from ransomware and deploying unified security platforms for visibility across networks. Vendors must align their offerings with federal compliance for cloud security solutions to participate.
- Key activities include securing supply chains for defense contractors, enhancing capabilities for detecting nation-state threats in real time, and mitigating insider threats in government networks. Operational readiness now depends on remediating zero-day vulnerabilities quickly, which is facilitated by automating security operations in federal SOCs and protecting sensitive data-in-transit and at-rest.
- Ultimately, these measures are crucial for building cyber resilience for public services, modernizing identity and access control systems, enhancing threat hunting with machine learning, and accelerating the adoption of secure access service edge for agencies.
What are the key market drivers leading to the rise in the adoption of US Government Cyber Security Industry?
- The transition to a zero trust architecture, driven by federal compliance mandates for continuous verification, is a primary driver of market growth.
- The market is driven by federal mandates for digital transformation services and the need for robust cybersecurity protection and response capabilities.
- The migration to secure cloud environments is a primary catalyst, with agencies leveraging these platforms to enhance security policy enforcement and achieve cross-domain visibility.
- This transition supports mission-critical defense strategies by enabling advanced threat visibility, where cloud-native tools provide a 40% faster detection rate for anomalous activity compared to on-premises legacy systems. The anticipated threat from quantum computing is accelerating investment in quantum-resistant algorithms.
- Furthermore, the integration of security information and event management systems is central to this modernization, with agencies relying on cybersecurity consulting services to deploy solutions that consolidate security data, improving analytical efficiency by at least 30%.
What are the market trends shaping the US Government Cyber Security Industry?
- A key market trend involves advancements in post-quantum cryptography, driving a focus on infrastructure readiness and the transition to quantum-resistant algorithms to secure national data.
- Emerging trends are reshaping the government cybersecurity market in US, with a strong emphasis on infrastructure modernization and creating a proactive defense posture. The adoption of a unified security fabric is gaining traction, with implementations showing a 25% improvement in threat correlation across disparate systems.
- This move toward identity-first security is complemented by the deployment of hardware-based security keys, which have reduced credential theft incidents by over 60% in pilot agencies. As government systems protection becomes more complex, agencies are increasingly relying on managed security services for specialized expertise.
- This is evident in areas like securing the public procurement platform and adhering to federal risk management frameworks, which now include rigorous disaster recovery protocols to ensure business continuity during cyber events.
What challenges does the US Government Cyber Security Industry face during its growth?
- A primary market challenge is the evolving complexity of automated and intelligent threats, which requires continuous adaptation of defensive strategies and technologies.
- A significant challenge facing the government cybersecurity market in US is the rising sophistication of automated reconnaissance and credential theft, which strains public sector IT infrastructure. Legacy systems often lack the capabilities for effective automated threat detection, increasing the time required for zero-day vulnerability remediation.
- This technical debt complicates real-time incident response, with studies showing that outdated enterprise security architecture can delay containment by over 72 hours. Managing supply chain risk management remains a persistent issue, as vulnerabilities in third-party software can undermine internal security controls. Moreover, the deployment of data loss prevention tools is often hindered by integration complexities.
- Effective insider threat detection and comprehensive business continuity planning are critical but require significant investment and skilled personnel, which remain scarce across federal agencies.
Exclusive Technavio Analysis on Customer Landscape
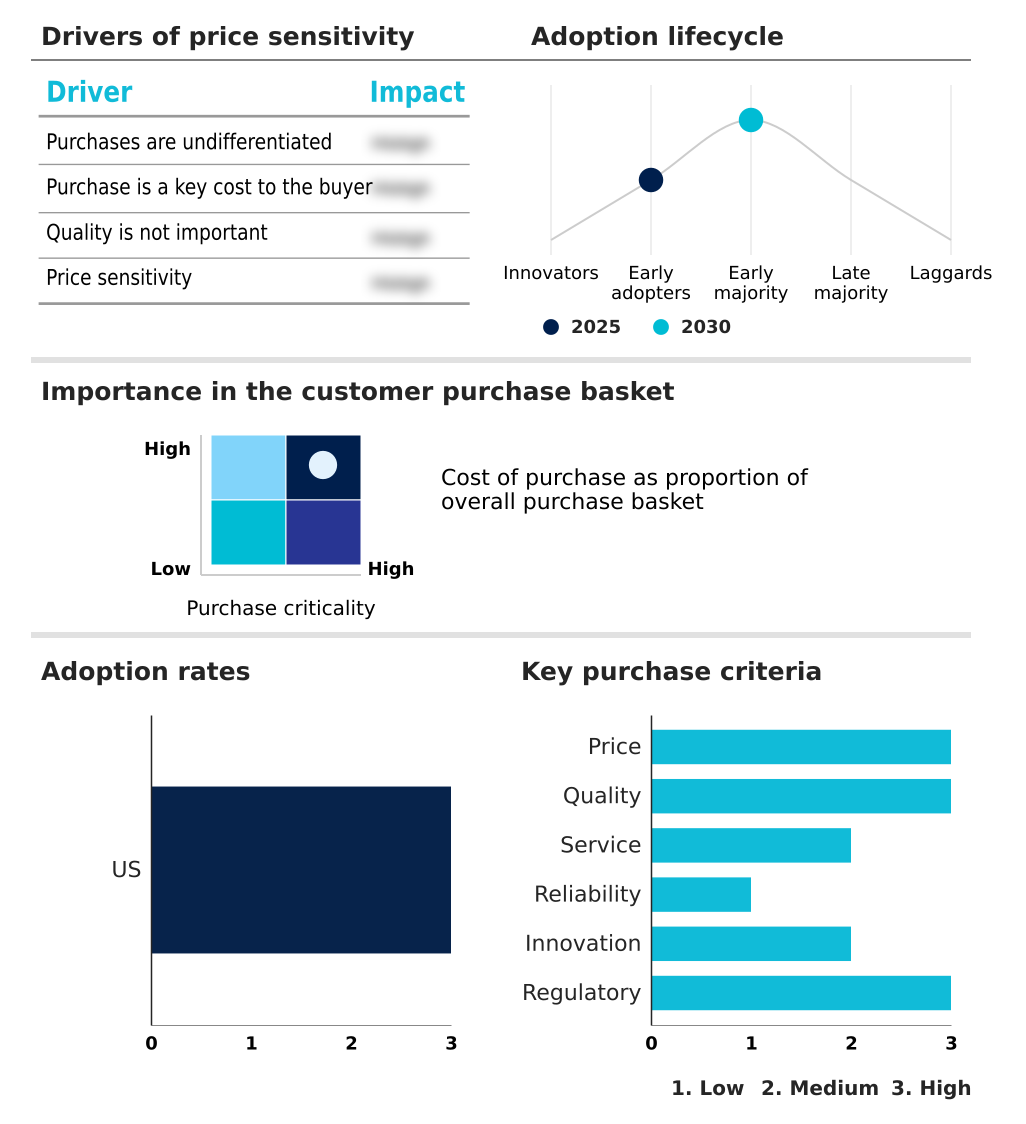
The us government cyber security market forecasting report includes the adoption lifecycle of the market, covering from the innovator’s stage to the laggard’s stage. It focuses on adoption rates in different regions based on penetration. Furthermore, the us government cyber security market report also includes key purchase criteria and drivers of price sensitivity to help companies evaluate and develop their market growth analysis strategies.
Customer Landscape of US Government Cyber Security Industry
Competitive Landscape
Companies are implementing various strategies, such as strategic alliances, us government cyber security market forecast, partnerships, mergers and acquisitions, geographical expansion, and product/service launches, to enhance their presence in the industry.
Accenture Plc - Delivering government cybersecurity consulting, risk management, and digital transformation services to public sector organizations.
The industry research and growth report includes detailed analyses of the competitive landscape of the market and information about key companies, including:
- Accenture Plc
- BitSight Technologies Inc.
- Booz Allen Hamilton Corp.
- Cisco Systems Inc.
- Cloudflare Inc.
- Coalfire Systems Inc.
- CrowdStrike Inc.
- Deloitte Touche Tohmatsu Ltd.
- Ernst and Young Global Ltd.
- Google LLC
- IBM Corp.
- Leidos Holdings Inc.
- Microsoft Corp.
- Optiv Security Inc.
- Palo Alto Networks Inc.
- PricewaterhouseCoopers LLP
- Proofpoint Inc.
- Qualys Inc.
- Rapid7 Inc.
- RTX Corp.
- Zscaler Inc.
Qualitative and quantitative analysis of companies has been conducted to help clients understand the wider business environment as well as the strengths and weaknesses of key industry players. Data is qualitatively analyzed to categorize companies as pure play, category-focused, industry-focused, and diversified; it is quantitatively analyzed to categorize companies as dominant, leading, strong, tentative, and weak.
Recent Development and News in Us government cyber security market
- In August 2024, the Cybersecurity and Infrastructure Security Agency issued a directive requiring federal agencies to begin implementing formal plans for migrating to post-quantum cryptography to ensure long-term data integrity.
- In August 2024, Microsoft announced that US government agencies began a significant consolidation of their identity management systems by adopting the Microsoft Entra ID platform to improve overall visibility and security.
- In March 2025, Palo Alto Networks announced a significant milestone in its support for federal modernization by achieving advanced certification for its unified security platforms across multiple government cloud regions.
- In April 2025, Palo Alto Networks announced a strategic expansion of its partnership with the US intelligence community to deploy advanced threat hunting capabilities across secure networks.
Dive into Technavio’s robust research methodology, blending expert interviews, extensive data synthesis, and validated models for unparalleled US Government Cyber Security Market insights. See full methodology.
| Market Scope | |
|---|---|
| Page number | 185 |
| Base year | 2025 |
| Historic period | 2020-2024 |
| Forecast period | 2026-2030 |
| Growth momentum & CAGR | Accelerate at a CAGR of 6.1% |
| Market growth 2026-2030 | USD 4475.1 million |
| Market structure | Fragmented |
| YoY growth 2025-2026(%) | 5.5% |
| Key countries | US |
| Competitive landscape | Leading Companies, Market Positioning of Companies, Competitive Strategies, and Industry Risks |
Research Analyst Overview
- The government cyber security market in US is defined by a strategic pivot toward proactive defense mechanisms, moving decisively beyond traditional perimeter security. A foundational element of this shift is the widespread adoption of zero trust architecture, coupled with advanced identity and access management and phishing-resistant mfa to secure a distributed hybrid workforce.
- Infrastructure modernization is now synonymous with deploying secure cloud environments and cloud native security platforms, which support crypto-agility frameworks essential for the eventual transition to post-quantum cryptography. Boardroom decisions are increasingly focused on achieving comprehensive vulnerability management, which has been shown to reduce breach impact costs by over 40%.
- Key technologies driving this evolution include unified security fabric for integrated oversight, dynamic network segmentation for granular control, and secure access service edge for unified policy enforcement. Operational capabilities are being enhanced through security information and event management (siem) systems, advanced endpoint protection, and data loss prevention tools.
- The focus is on enabling real-time incident response through autonomous response capabilities, automated threat detection, and continuous monitoring, all fueled by actionable cyber threat intelligence and sophisticated threat hunting. This complex ecosystem relies on a combination of managed security services, digital transformation services, and mission-critical cryptographic solutions to manage supply chain risk and counter nation-state threats.
What are the Key Data Covered in this US Government Cyber Security Market Research and Growth Report?
-
What is the expected growth of the US Government Cyber Security Market between 2026 and 2030?
-
USD 4.48 billion, at a CAGR of 6.1%
-
-
What segmentation does the market report cover?
-
The report is segmented by End-user (US intelligence community, Department of homeland security, and Department of defense), Deployment (On-premises, and Cloud-based), Product (Services, and Solutions) and Geography (North America)
-
-
Which regions are analyzed in the report?
-
North America
-
-
What are the key growth drivers and market challenges?
-
Transition to zero trust architecture and federal compliance, Evolving complexity of automated and intelligent threats
-
-
Who are the major players in the US Government Cyber Security Market?
-
Accenture Plc, BitSight Technologies Inc., Booz Allen Hamilton Corp., Cisco Systems Inc., Cloudflare Inc., Coalfire Systems Inc., CrowdStrike Inc., Deloitte Touche Tohmatsu Ltd., Ernst and Young Global Ltd., Google LLC, IBM Corp., Leidos Holdings Inc., Microsoft Corp., Optiv Security Inc., Palo Alto Networks Inc., PricewaterhouseCoopers LLP, Proofpoint Inc., Qualys Inc., Rapid7 Inc., RTX Corp. and Zscaler Inc.
-
Market Research Insights
- The market dynamics are shaped by stringent federal cybersecurity compliance and a push for greater digital resilience frameworks. Adherence to FedRAMP high authorization for cloud services has become a critical benchmark, with certified platforms showing a 30% faster deployment time compared to non-compliant alternatives.
- The emphasis on CMMC certification requirements for the defense industrial base has streamlined security protocols, reducing breach incident rates by up to 20% among early adopters. Protecting critical infrastructure now involves robust threat intelligence sharing, which has improved nation-state threat detection capabilities across agencies.
- This focus on unified security standards and proactive defense posture is essential for safeguarding national security data and ensuring the integrity of government systems against sophisticated cyber threats.
We can help! Our analysts can customize this us government cyber security market research report to meet your requirements.

 RIA -
RIA - 
